Today I’m going to discuss how you can get a free SSL cert from Let’s Encrypt, and then use it on a Windows Server.
In my example I will be using the free SSL cert for a remote Desktop Collection!
Requirements:
The latest powershell is required so you can utilize the “install-module” command, this can be found here.
https://www.microsoft.com/en-us/download/details.aspx?id=50395
For server 2012 R2 x64 choose this one “Win8.1AndW2K12R2-KB3134758-x64.msu”.
This is at the last option after clicking the download button.
Before we begin you should know that the method to proving the ownership of the domain I chose is ‘dns-01’ this method requires you to create a txt DNS record. This was the easiest way for me. I’m going to create one with you now for my domain, techstat.net
Now run powershell as admin, paste the following commands and fill out the following variables.
the script:
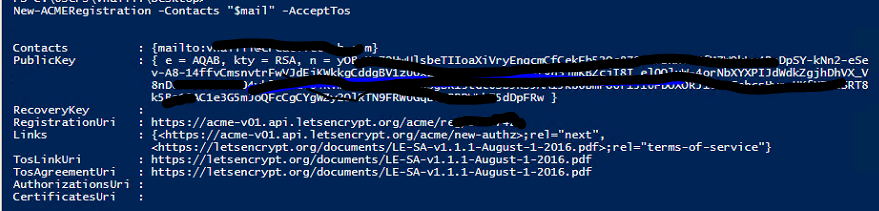
$domain = "yourdomain.com" #if you need a cert for a subdomain then you should put the subdomain not the root $mail = "mailto:youremail@domain.com" #note this email does not need to be under the domain you are registering, you can use live.com or gmail.com $domalias = "domain" #any name is fine $certalias = "domaincert" #any name is fine $certloc = "C:\certfiles\$domalias" Install-Module ACMESharp # you should have the latest powershell version to use this Import-Module ACMESharp Initialize-ACMEVault #this command is only required once per session New-ACMERegistration -Contacts "$mail" -AcceptTos New-ACMEIdentifier -Dns $domain -Alias $domalias Complete-ACMEChallenge $domalias -ChallengeType dns-01 -Handler manual Write-Host -fore yellow "Copy your TXt record values from above, then add to your domain DNS then press enter here" Pause Submit-ACMEChallenge $domalias -ChallengeType dns-01 Write-Host -ForegroundColor yellow "This script will pause for 60 seconds while it waits for your request to be submitted, then it will update." Start-Sleep 60 Update-ACMEIdentifier $domalias Write-Host -fore yellow "If the above says the status is valid, then press enter, if it says invalid review your settings, if it says pending just rerun the update command above in the script" Pause New-ACMECertificate $domalias -Generate -Alias $certalias Submit-ACMECertificate $certalias Write-Host -ForegroundColor yellow "This script will pause for 60 seconds while it waits for your request to be submitted, then it will update." Start-Sleep 60 Update-ACMECertificate $certalias new-item -ItemType Directory "$certloc" Get-ACMECertificate $certalias -ExportKeyPEM "$certloc\privatekey.key.pem" Get-ACMECertificate $certalias -ExportCsrPEM "$certloc\certcsr.csr.pem" Get-ACMECertificate $certalias -ExportIssuerPEM "$certloc\issuer.crt.pem" -ExportIssuerDER "$certloc\issuer.crt" Get-ACMECertificate $certalias -ExportPkcs12 "$certloc\cert.pfx" -CertificatePassword 'P@ss1234' write-host -ForegroundColor yellow "your .pfx file was saved with the pass P@ss1234"
Explaining the Let’s Encrypt Script and Module
I’m assuming you’ve already upgraded powershell with the link I provided. Then you should have installed the module via the command. Then you should have imported the module. Finially you should have ran the initialize command (this command is only required once).
The email registration doesn’t send you anything, it just ties the domain to your email (email must be valid, can be any domain)
Then we create the domain identifier and bond it to an alias
This is the complete acme challenge part, the name is tricky, it doesn’t actually complete. It actually begins the challenge.
At this step you are given the txt record name and value that you will need to setup.
My TXT record will be called “_acme-challenge” and the Value will be whatever is in the value field, minus the brackets.
Since my domain is hosted with Cloudflare this is what my record looked like.
Once I hit enter in the script it will submit my challenge, then pause for 60 seconds, if you see a “status” of pending, that means you did everything well so far.
This update-acmeidentifier command just gets the status of a challenge you submitted.
If everything went well then after those long 60 seconds the script will now show a status of “valid” like below.
If it did not then you need to find the error in the config. If it shows “invalid” you have a problem. Most likely you messed up the DNS record or it hasn’t showed up yet.
Then the alias for the cert is created, submitted, and checked.
Then the folder structure is created in C:\ with the “new-item” command.
Once that’s done it will actually do the exporting.
Once all of that is done you should get all the cert files in a directory on the C:\ drive called certfiles.
I used the script for a RDSH collection test-lab, I was able to easily add the cert with the password in Server Manager.
Note: the password is required or else you’ll have “delegation” errors.
Renewels: As it stands there’s no way with powershell to renew your certs, once that feature comes out I will update this!