With code 9.7 released Cisco decided to add two VERY important features. Route based VPN with VTIs, and bridge groups! This article will show a quick configuration of a route based VPN with ASAs! Previously to do something like this you would need to build a GRE tunnel over IPSEC with a second router terminating GRE.
Notice: Currently OSPF, and EIGRP are not yet supported to run over the tunnel interface. Even with the static neighborship command. The tunnel interface won’t turn to a point-to-point link. So as of 2/19/2017 we must use BGP to advertise over this tunnel. Or we can just use static routes. Also BFD is not supported on the tunnel interfaces yet.
Update: as of 9.9.2 BGP is still the only supported protocol, which is not really an issue as we can always redistribute
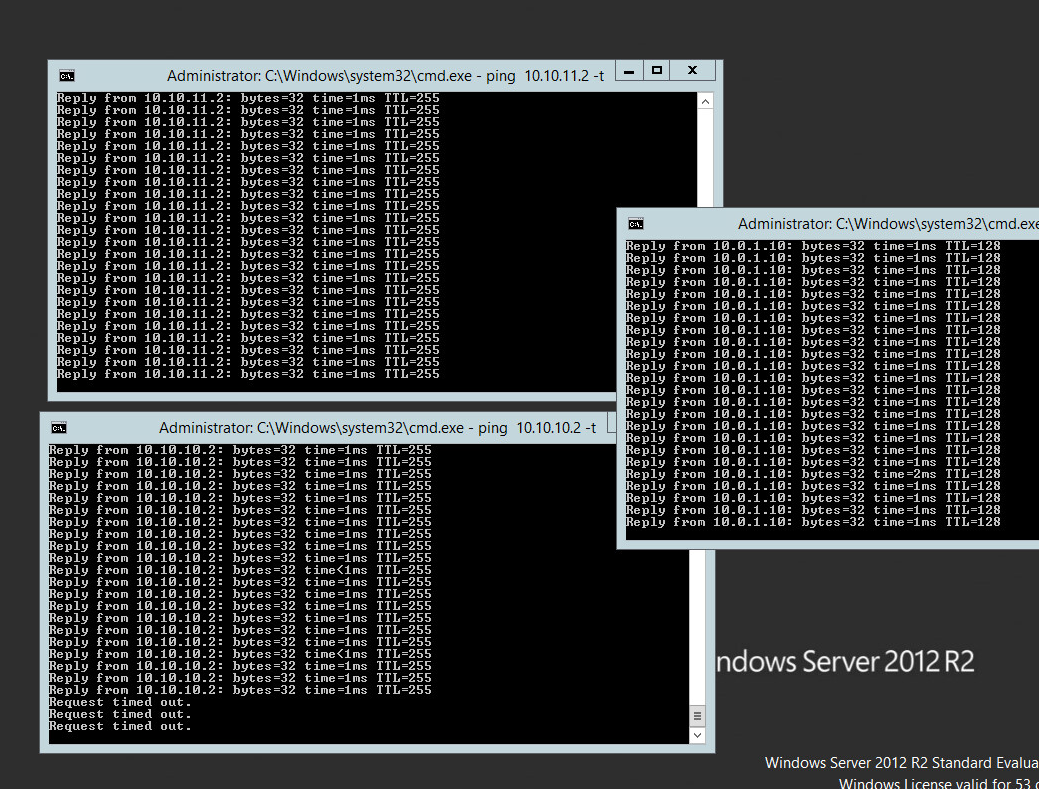
I was able to get this to work with 0 packet loss!
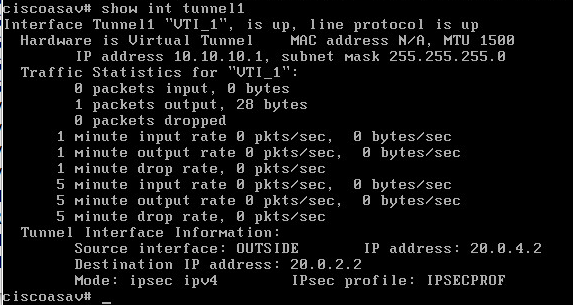
Here’s a tease of an up VTI!
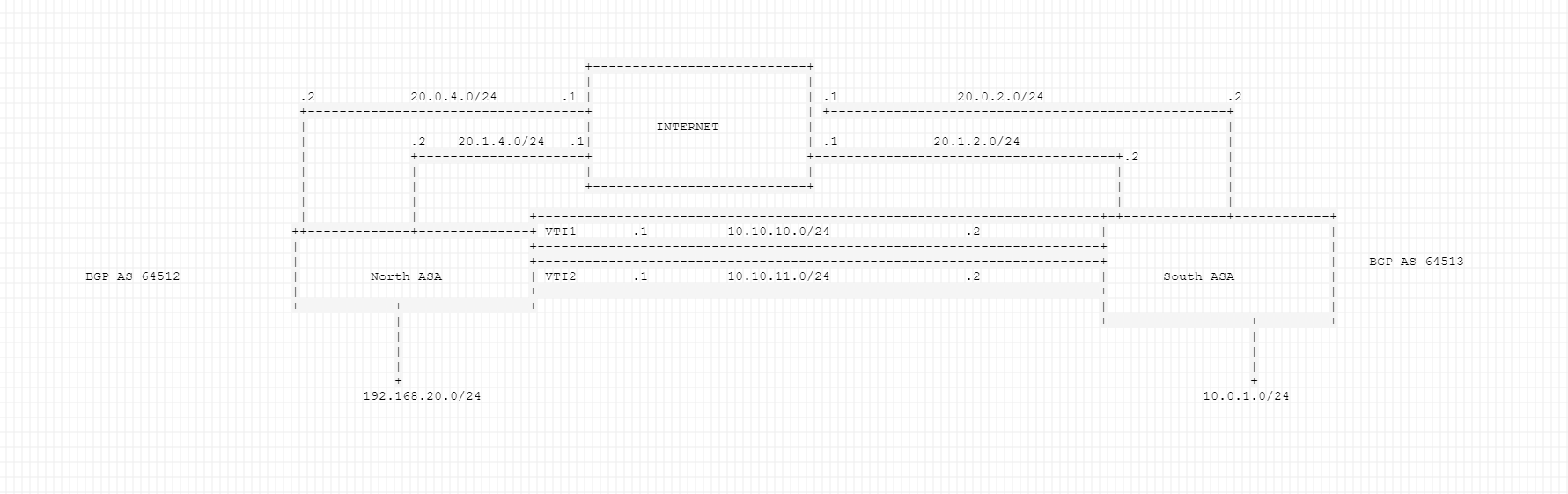
Network Diagram:
First of all let’s apply some good practice config’s to make this tunnel a little more stable and perform better.
Apply the following to both ASA’s:
enable conf t sysopt connection tcpmss 1350 sysopt connection preserve-vpn-flows
the first command clamps the TCP MSS/payload to 1350 bytes, and the second command keeps stateful connections even if the vpn temporarily drops.
North ASA config:
en conf t group-policy tunnelGP internal group-policy tunnelGP attributes vpn-session-timeout none vpn-idle-timeout none vpn-tunnel-protocol ikev1 exit tunnel-group 20.0.2.2 type ipsec-l2l tunnel-group 20.0.2.2 general-attributes default-group-policy tunnelGP tunnel-group 20.0.2.2 ipsec-attributes ikev1 pre-shared-key PASSWORD isakmp keepalive threshold 10 retry 2 exit tunnel-group 20.1.2.2 type ipsec-l2l tunnel-group 20.1.2.2 general-attributes default-group-policy tunnelGP tunnel-group 20.1.2.2 ipsec-attributes ikev1 pre-shared-key PASSWORD isakmp keepalive threshold 10 retry 2 exit crypto ipsec ikev1 transform-set TUNNELTRANS esp-aes esp-sha-hmac crypto ipsec profile IPSECPROF set ikev1 transform-set TUNNELTRANS set pfs group2 set security-association lifetime kilobytes unlimited set security-association lifetime seconds 86400 exit ########VTI Configuration for both WAN circuits int Tunnel1 nameif VTI_1 ip address 10.10.10.1 255.255.255.0 tunnel source interface OUTSIDE tunnel destination 20.0.2.2 tunnel mode ipsec ipv4 tunnel protection ipsec profile IPSECPROF exit int Tunnel2 nameif VTI_2 ip address 10.10.11.1 255.255.255.0 tunnel source interface OUTSIDE2 tunnel destination 20.1.2.2 tunnel mode ipsec ipv4 tunnel protection ipsec profile IPSECPROF exit #########bgp config with multipath router bgp 64513 address-family ipv4 unicast neighbor 10.10.10.2 remote-as 64512 neighbor 10.10.11.2 remote-as 64512 neighbor 10.10.10.2 next-hop-self neighbor 10.10.11.2 next-hop-self network 192.168.20.0 mask 255.255.255.0 neighbor 10.10.10.2 activate neighbor 10.10.11.2 activate maximum-paths 2 exit-address-family bgp graceful-restart route outside2 20.1.2.2 55.255.255.255 20.1.4.1
South ASA config:
en conf t group-policy tunnelGP internal group-policy tunnelGP attributes vpn-session-timeout none vpn-idle-timeout none vpn-tunnel-protocol ikev1 exit tunnel-group 20.0.4.2 type ipsec-l2l tunnel-group 20.0.4.2 general-attributes default-group-policy tunnelGP tunnel-group 20.0.4.2 ipsec-attributes ikev1 pre-shared-key PASSWORD isakmp keepalive threshold 10 retry 2 exit tunnel-group 20.1.4.2 type ipsec-l2l tunnel-group 20.1.4.2 general-attributes default-group-policy tunnelGP tunnel-group 20.1.4.2 ipsec-attributes ikev1 pre-shared-key PASSWORD isakmp keepalive threshold 10 retry 2 exit crypto ipsec ikev1 transform-set TUNNELTRANS esp-aes esp-sha-hmac crypto ipsec profile IPSECPROF set ikev1 transform-set TUNNELTRANS set pfs group2 set security-association lifetime kilobytes unlimited set security-association lifetime seconds 86400 exit ########VTI tunnel configuration for both WANs int Tunnel1 nameif VTI_1 ip address 10.10.10.2 255.255.255.0 tunnel source interface OUTSIDE tunnel destination 20.0.4.2 tunnel mode ipsec ipv4 tunnel protection ipsec profile IPSECPROF exit int Tunnel2 nameif VTI_2 ip address 10.10.11.2 255.255.255.0 tunnel source interface OUTSIDE2 tunnel destination 20.1.4.2 tunnel mode ipsec ipv4 tunnel protection ipsec profile IPSECPROF exit ###########BGP config with multipath router bgp 64512 address-family ipv4 unicast neighbor 10.10.10.1 remote-as 64513 neighbor 10.10.11.1 remote-as 64513 neighbor 10.10.10.1 next-hop-self neighbor 10.10.11.1 next-hop-self network 10.0.1.0 mask 255.255.255.0 neighbor 10.10.10.1 activate neighbor 10.10.11.1 activate maximum-paths 2 exit-address-family bgp graceful-restart route outside2 20.1.4.2 255.255.255.255 20.1.2.1 1
Note: As of code 9.8.1 IKEv2 is now supported as well, if you’re interested in the IKEv2 version for the config, please see below:
assume this is just one side and the wan on the other ASA’s WAN IP is 2.0.0.2 in the below example.
crypto ipsec ikev2 ipsec-proposal vtiproposal protocol esp encryption aes-192 protocol esp integrity sha-1 exit crypto ipsec profile vtiprofile set ikev2 ipsec-proposal vtiproposal exit int tunnel 1 nameif vti ip add 10.0.0.1 255.255.255.0 tunnel source int outside tunnel destination 2.0.0.2 tunnel mode ipsec ipv4 tunnel protection ipsec profile vtiprofile exit tunnel-group 2.0.0.2 type ipsec-l2l tunnel-group 2.0.0.2 ipsec-attributes ikev2 remote-auth pre-shared-key password ikev2 local-auth pre-shared-key password exit group-policy tunnelGP internal group-policy tunnelGP attributes vpn-tunnel-protocol ikev2 exit tunnel-group 2.0.0.2 general-attributes default-group-policy tunnelGP exit crypto ikev2 policy 1 encryption aes-192 integrity sha group 14 prf sha exit crypto ikev2 enable outside
Let’s discuss the config above. There’s a lot going on here. Eachtunnel interface gets its own tunnel-group. They are sharing an ipsec profile. The VTI’s subnets are 10.10.10.0/24 and 10.10.11.0/24. With the VTIs up we now have point to point links we can route over to the other side. Static OSPF or EIGRP neighborships would fit best here. However like I said above they are not supported yet. Thus we need to use BGP. We then configured BGP with private ASNs. We then advertised the LAN subnets to our neighbors and made sure the ASA is their next hop. The BGP feature added was maximum-paths to allow for per session load balancing. We need the static routes for the secondary tunnels because our default route is pointintg towards ISP 1. If we don’t have it then our secondary tunnels will need to renegotiate and failover won’t be so smooth.
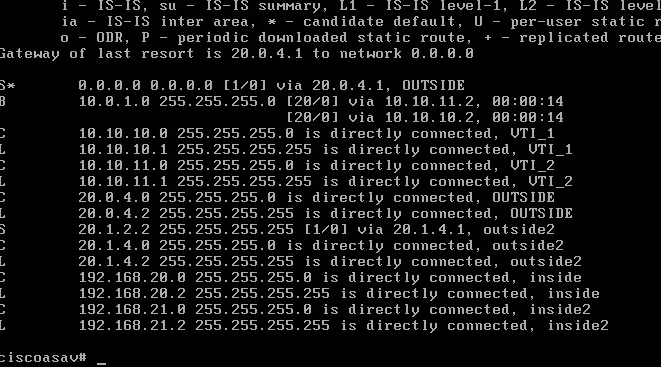
Here’s what the routing table looks like now from the North ASA. Notice the BGP route listed twice? That’s because we enabled multipath/maximum paths.
Now let’s test failing over the tunnel interfaces by shutting down the WAN.
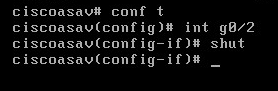
Notice the second tunnel is still up

We get no ping loss to a host on the other wend of the other ASA, 10.0.1.10.
Cisco documentation for reference